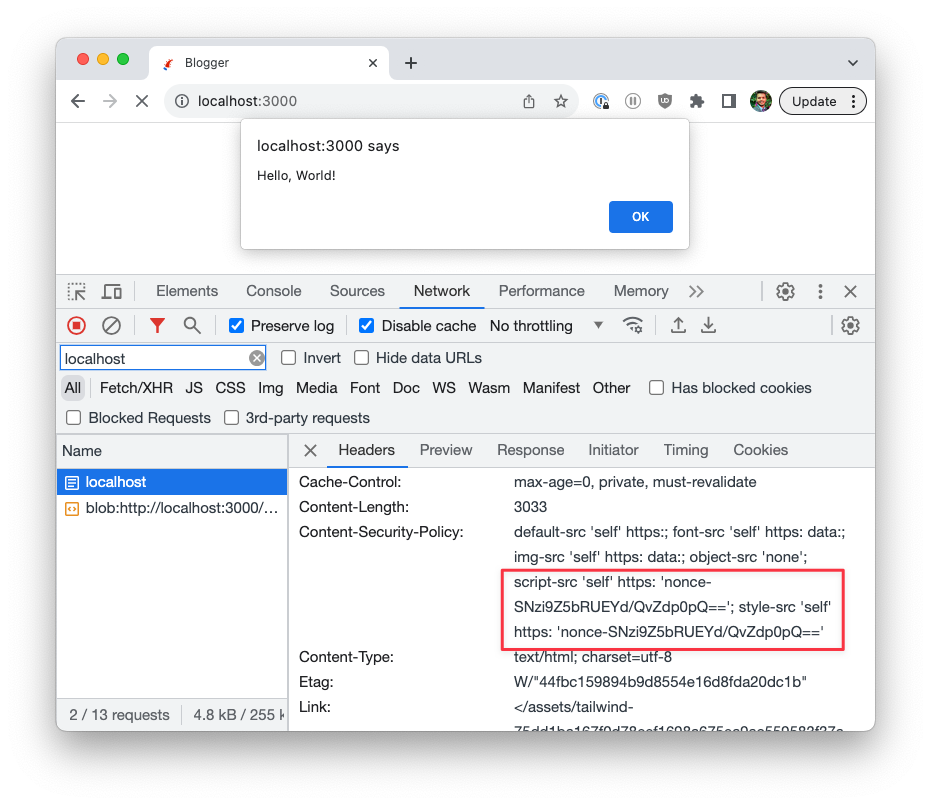
⚖ Content Security Policy: 'nonce-value' cancels 'unsafe-inline' in script-src and prohibits the execution of inline scripts without nonce=value attribute

⚖ The 'nonce-value' allows any host-sources for external scripts and allows inline scripts without 'unsafe-inline' in the script-src, 'nonce-value' is case-sensitive

Improving application security in ASP.NET Core Razor Pages using HTTP headers – Part 1 | Software Engineering

⚖ The 'nonce-value' allows any host-sources for external scripts and allows inline scripts without 'unsafe-inline' in the script-src, 'nonce-value' is case-sensitive
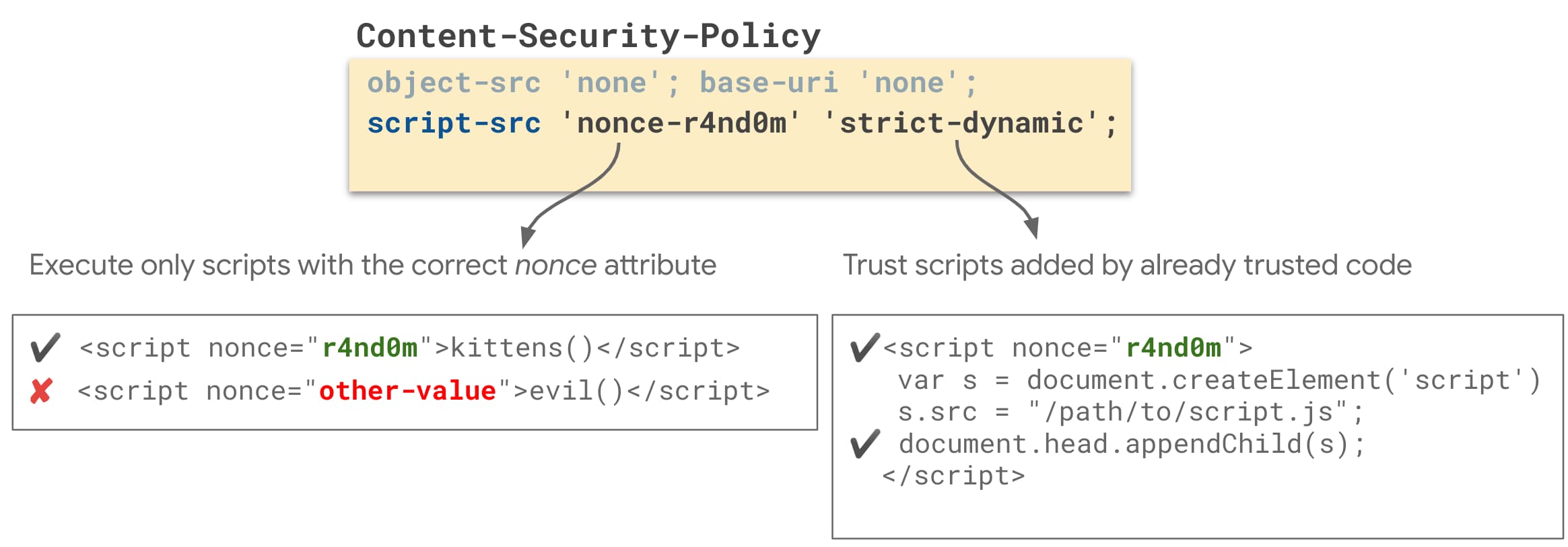
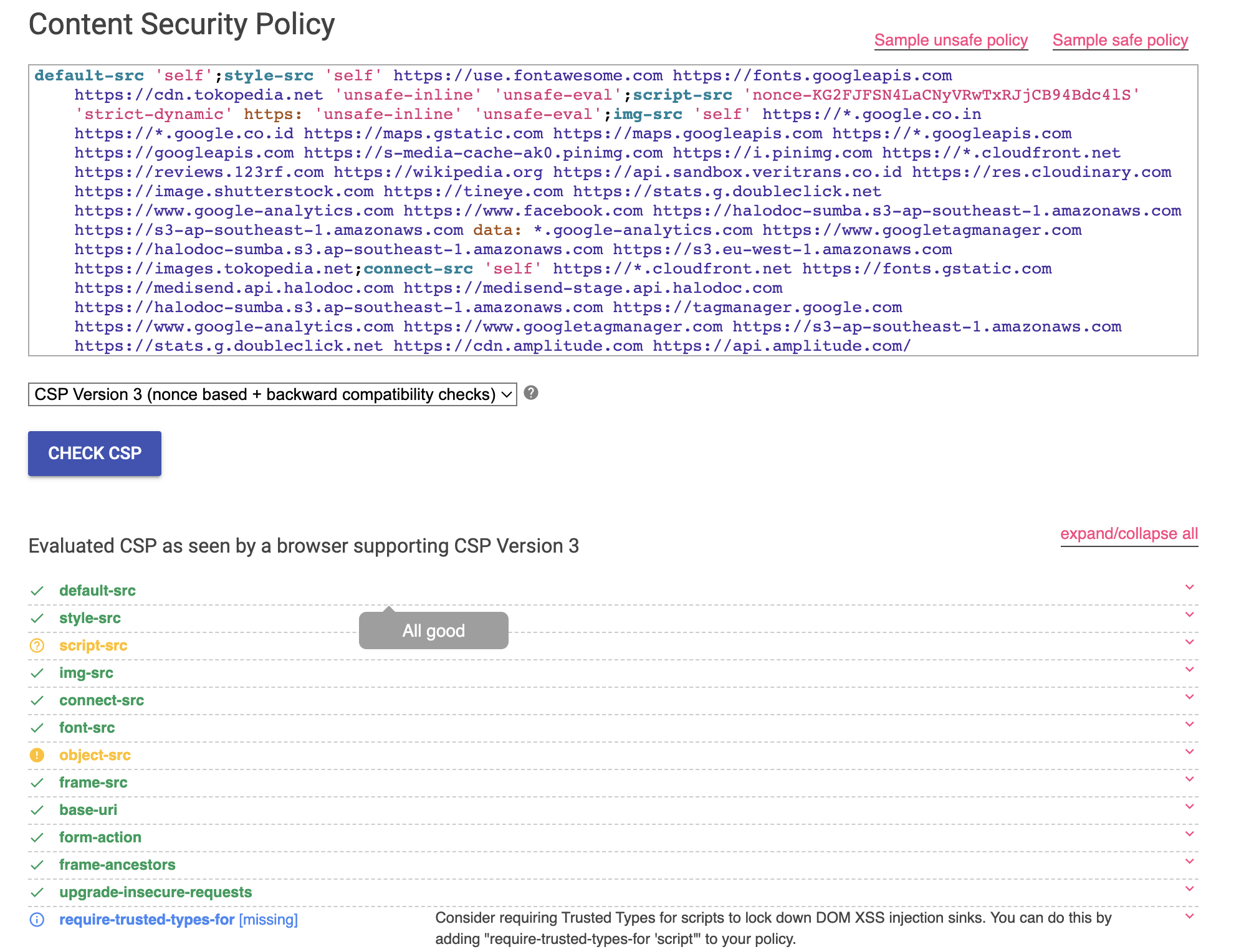
Mitigate cross-site scripting (XSS) with a strict Content Security Policy ( CSP) | Articles | web.dev

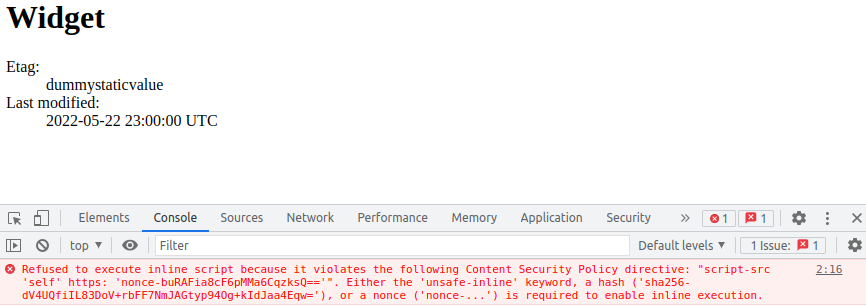
Parse Dashboard 5.0.0 / Insecure ContentSecurityPolicy (CSP) - Parse Dashboard - Parse Community Forum

⚖ Content Security Policy: both 'nonce-value' and 'hash-value' in the style-src directive, which one is higher priority
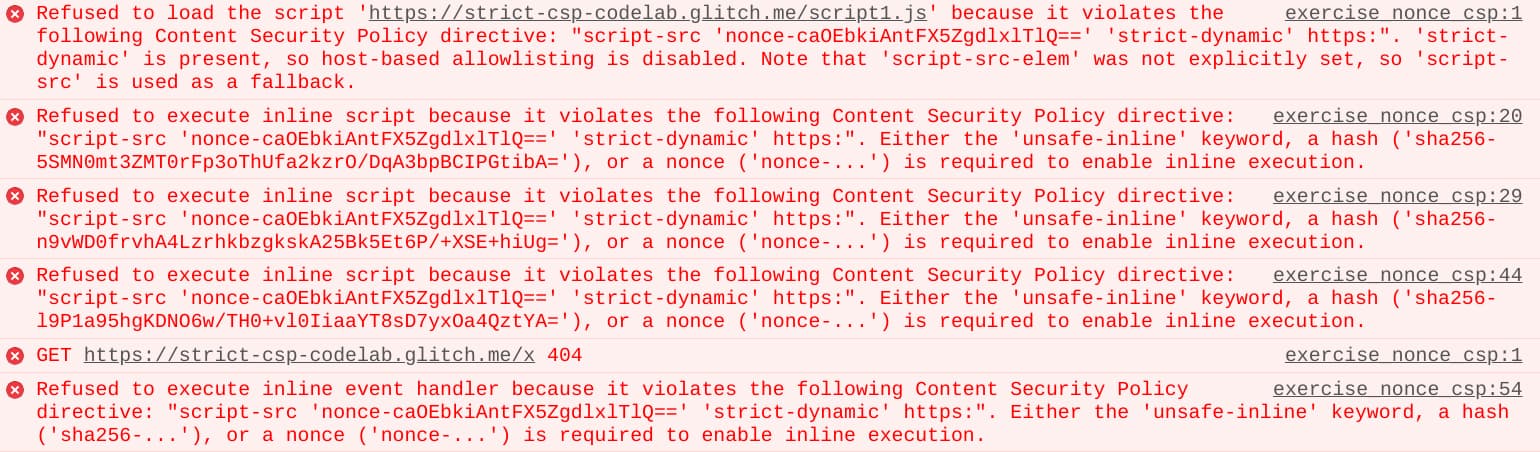
Mitigate cross-site scripting (XSS) with a strict Content Security Policy ( CSP) | Articles | web.dev

Mitigate cross-site scripting (XSS) with a strict Content Security Policy ( CSP) | Articles | web.dev